Article
Apr 5, 2026
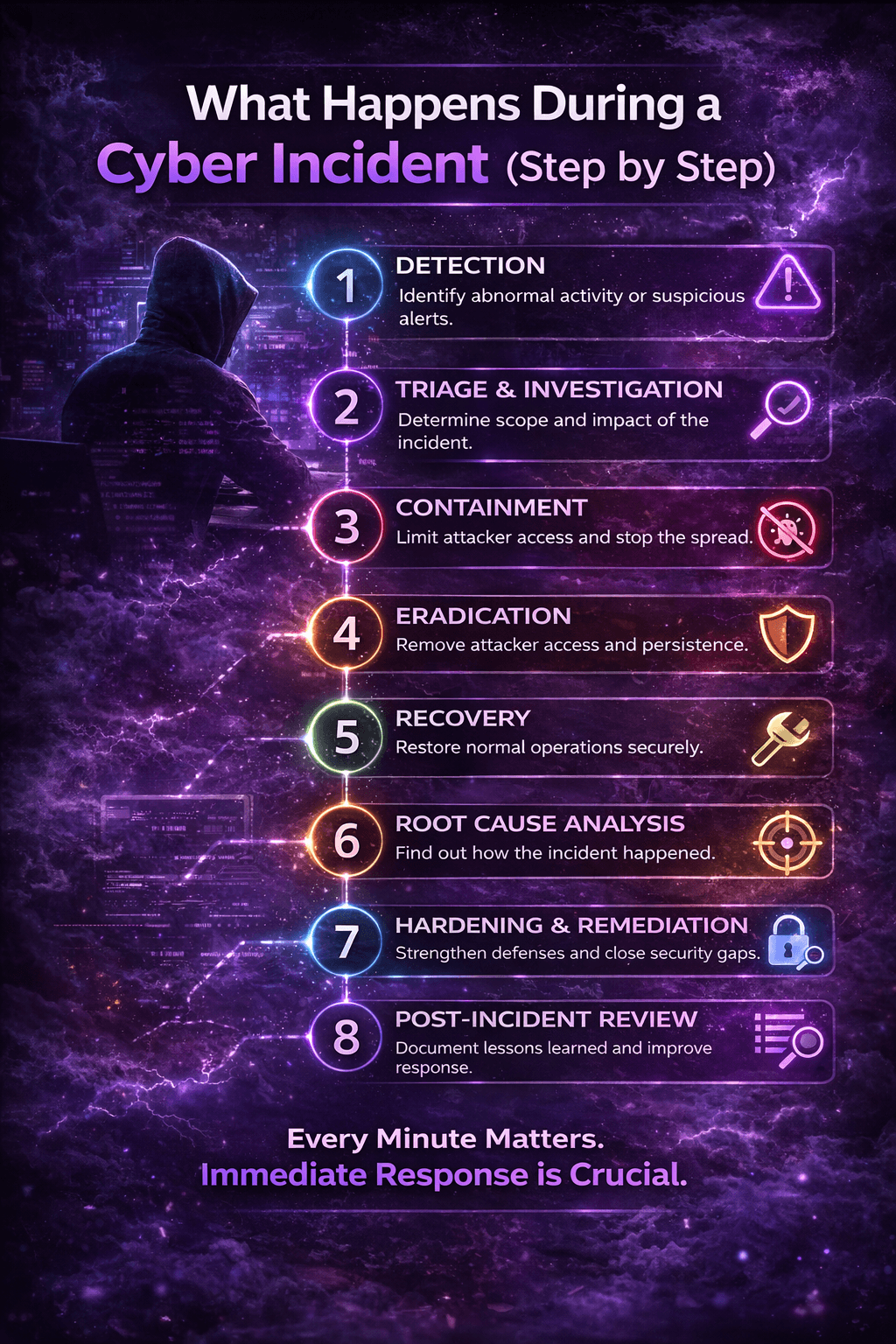
What Happens During a Cyber Incident (Step-by-Step)
A step-by-step breakdown of what actually happens during a cyber incident—from initial detection to full recovery—highlighting the critical actions that determine whether an attack is contained or escalates into a breach.
Title
What Happens During a Cyber Incident (Step by Step)
Short Description
When a cyber incident hits, every minute matters. This guide walks through what actually happens during an incident, from detection and containment to recovery and hardening.
Content
Introduction
Most organizations do not have a cyber incident problem. They have a response problem.
The damage caused by an incident often comes down to how quickly it is detected, how fast it is contained, and whether anyone takes ownership early enough to stop it from spreading.
This article breaks down what actually happens during a cyber incident, step by step, so you can understand what matters most when time is working against you.
1. Detection
Every incident starts with a signal.
That signal might be:
A suspicious login
A phishing report
Malware detected on an endpoint
A user reporting unusual account activity
Alerts from identity, endpoint, or cloud security tools
At this stage, the goal is simple: determine whether the activity is real, how serious it is, and what systems or users may be affected.
The faster this is validated, the faster the response can begin.
2. Triage and Investigation
Once suspicious activity is identified, the next step is triage.
This means understanding:
What happened
When it started
Which user, device, or system is involved
Whether the attacker still has access
Whether the activity is isolated or spreading
During this phase, responders review:
Sign-in logs
Endpoint activity
Email rules
MFA changes
Token usage
Device and session behavior
The goal is to separate noise from real compromise and define the scope as quickly as possible.
3. Containment
Containment is where response becomes action.
If an attacker is active, responders move immediately to limit or remove access. This may include:
Disabling a compromised account
Revoking active sessions
Isolating an endpoint
Blocking malicious IP addresses
Removing forwarding rules
Restricting access through Conditional Access or policy changes
Containment is time-sensitive. Delays allow attackers to establish persistence, move laterally, or exfiltrate data.
This is often the difference between a contained incident and a full breach.
4. Eradication
Once the threat is contained, responders focus on removing the attacker's foothold.
This may involve:
Deleting malicious inbox rules
Removing unauthorized devices
Revoking attacker-granted permissions
Rotating credentials
Re-securing MFA methods
Removing persistence mechanisms
The goal is to ensure the attacker cannot regain access through the same path.
Eradication is not just about stopping visible activity. It is about removing everything that allowed the compromise to survive.
5. Recovery
After the environment is stabilized, recovery begins.
This phase focuses on restoring normal operations safely. Depending on the incident, that may include:
Re-enabling accounts
Reconnecting isolated devices
Validating systems before returning them to production
Confirming that user access is secure
Monitoring for re-entry attempts
Recovery should never be rushed. If the environment is brought back too early, attackers may still have a path in.
6. Root Cause Analysis
Containment and recovery are not enough if no one identifies how the incident happened in the first place.
Root cause analysis answers questions like:
Did the attacker get in through phishing?
Was MFA bypassed?
Was there a weak Conditional Access policy?
Did a privileged account have too much access?
Was a session token stolen?
Was there a detection gap?
This step is critical because it tells you whether the same incident could happen again tomorrow.
7. Hardening and Remediation
Once the root cause is clear, the environment must be hardened.
This may include:
Tightening Conditional Access policies
Enforcing stronger MFA controls
Reducing privileged access
Locking down email forwarding
Improving monitoring rules
Updating response playbooks
Training users based on what actually happened
This is where incident response becomes long-term security improvement.
Without remediation, the same weaknesses remain open.
8. Post-Incident Review
Every incident should end with a review.
This review should document:
What happened
What was impacted
How the attacker gained access
What actions were taken
What gaps were identified
What changes were made afterward
The purpose is not just reporting. It is learning.
Organizations that treat every incident as a chance to improve become harder to compromise over time.
Final Thoughts
A cyber incident is not just a technical problem. It is a time-sensitive operational problem.
The organizations that recover best are the ones that can detect quickly, respond decisively, and take ownership before the incident grows.
When an attack is active, the process matters. Speed matters. Ownership matters.
That is what turns a live incident into a contained event instead of a major breach.