Article
Apr 3, 2026
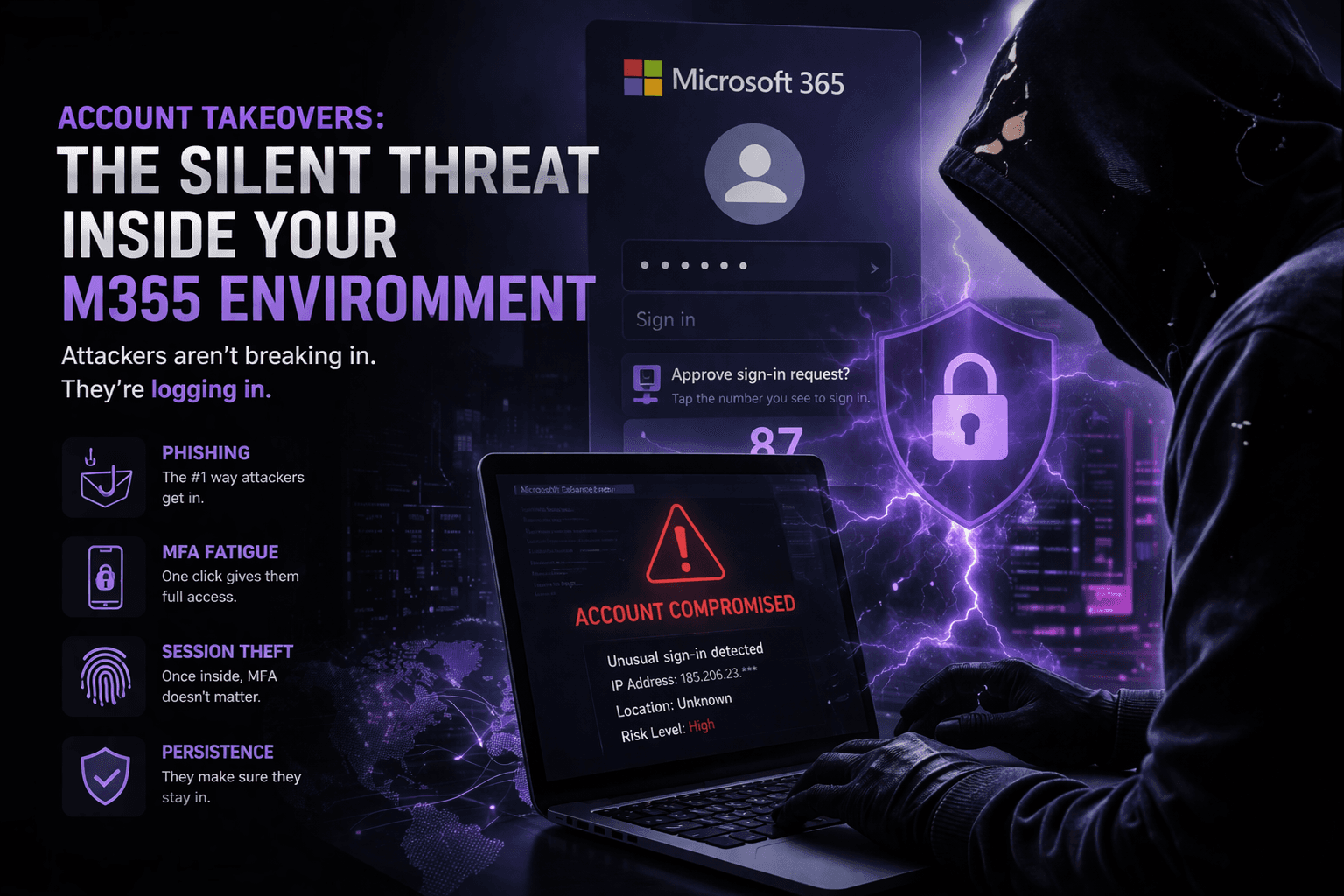
How Account Takeovers Actually Happen And How to Stop Them
Account takeovers are one of the most common and damaging attacks targeting businesses today. Attackers use phishing, MFA fatigue, token theft, and weak Microsoft 365 configurations to gain access and stay there. In this article, we break down how account takeovers actually happen, what warning signs to look for, and how to stop them before they turn into a full breach.
Introduction
Account takeovers (ATO) are one of the most common and damaging attacks targeting organizations today.
Most environments are not breached through exploits. They are accessed using valid credentials.
Many organizations assume they are protected because MFA is enabled. In reality, attackers bypass these controls every day using phishing, token theft, and MFA fatigue techniques.
This article breaks down how account takeovers actually happen, what attackers look for, and how to stop them before they escalate into a full breach.
How Account Takeovers Actually Happen
Phishing (Initial Access)
Most attacks begin with a phishing email designed to look legitimate. These emails often impersonate Microsoft, internal IT teams, or trusted vendors.
Users are directed to a fake login page and unknowingly submit their credentials, giving attackers initial access.
MFA Fatigue / Push Spam
If MFA is enabled, attackers attempt to bypass it using push fatigue techniques:
Sending repeated MFA prompts
Relying on user confusion or frustration
Waiting for a single approval
Once approved, the attacker gains access to the account.
Session Hijacking / Token Theft
In more advanced attacks, attackers steal session tokens.
This allows them to:
Access the account without re-authentication
Bypass MFA entirely
Maintain access even after credentials are changed
Establishing Persistence
After gaining access, attackers move quickly to maintain control:
Creating inbox forwarding rules
Adding new MFA methods
Registering new devices
Granting application or delegated permissions
This ensures they retain access even if the initial compromise is discovered.
Signs You May Have Been Compromised
Look for:
Logins from unusual locations or IP addresses
Multiple failed login attempts followed by success
Unexpected or repeated MFA prompts
New inbox rules or external forwarding
Suspicious emails sent from internal users
How to Prevent Account Takeovers
Enforce Strong MFA
Use number matching or phishing-resistant MFA methods where possible.
Implement Conditional Access
Block high-risk locations
Require compliant or trusted devices
Enforce risk-based authentication policies
Monitor Sign-In Activity
Continuously monitor login behavior and investigate anomalies immediately.
Lock Down Email Rules
Prevent automatic forwarding to external domains and monitor for rule creation.
Limit Privileged Access
Reduce the number of global administrators and enforce least privilege.
Use Endpoint and Identity Protection
Leverage tools such as Microsoft Defender to detect suspicious activity across identities and endpoints.
What to Do If an Account Is Compromised
Immediate response is critical:
Disable the account
Revoke all active sessions
Reset credentials
Remove malicious inbox rules
Review sign-in logs and activity
Re-secure MFA and authentication methods
Delays in response allow attackers to expand access, exfiltrate data, and establish long-term persistence.
Final Thoughts
Account takeovers are not theoretical. They happen every day and often succeed due to small gaps in configuration, visibility, or response.
The difference between a contained incident and a full breach comes down to one thing:
Speed of detection and response.